Welcome to the Fall 2021 edition of the Quarterly Security Reminders email, brought to you by Wright State's Chief Information Security Officer. This quarter's newsletter will provide you with important information about ransomware.
Ransomware: What is it?
The term ransomware has been in the news quite a lot over the past year or so. Many businesses, as well as government agencies and universities, have been significantly impacted by these types of attacks. One notable ransomware attack hit the Colonial Pipeline, which led to its operations being shut down for several days. It has been reported that a ransom of 5 million dollars was paid in order to regain functionality. The federal government recommends not paying such ransoms, but losing access to critical files and systems has left some institutions with no other choice.
Most modern ransomware not only encrypts files on the computer system it infects, it also steals the files and saves them on servers controlled by the perpetrators of the attack. This causes further complications for the university if there is sensitive data contained within the files. This would constitute a data breach resulting in real dollar costs to the university. For instance, this may require us to provide identity theft protection to individuals impacted by the data breach. Additionally, damage to the university's reputation and public image would likely occur.
You might be wondering how you can protect your WSU files and systems against ransomware attacks. There are three key ways to protect yourself:
- Check to see that you have SentinelOne installed on your WSU -provided computer. SentinelOne provides protection against ransomware attacks by not only providing advanced anti-malware protection, but also by backing up your files to a location the ransomware cannot reach.
- Store your important files on your H, K, or R drives which are backed up nightly allowing those files to be restored should an attack find a way around our defenses.
- Remain vigilant against potential phishing emails, as it continues to be the primary method to initiate ransomware attacks against organizations.
SentinelOne
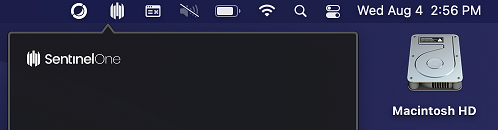
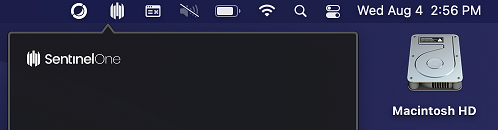
Computer systems distributed by CaTS will have SentinelOne installed at the time the computer is configured for you. Check if SentinelOne is operating on your computer using the steps below:
PC Users: The SentinelOne icon should appear in the hidden icons menu in the bottom righthand corner of your screen.

Mac Uers: The SentinelOne icon should appear in the top righthand corner of your screen.\
Additionally, you can contact the CaTS Help Desk at 937-775-4827 and they can quickly check to determine if the program is installed.